Scammers are increasingly exploiting tap-to-pay and NFC technologies to illicitly skim funds from credit cards and mobile wallets. Understanding this threat is the first step to protecting your finances.
Key Takeaways:
- NFC and tap-to-pay systems can be vulnerable to remote skimming.
- Simple physical barriers can prevent unauthorized transactions.
- Digital security practices complement physical protection.
- Awareness is your strongest defense against these evolving scams.
Understanding the ‘Ghost Tap’ Threat
The convenience of contactless payments comes with a hidden risk: ‘ghost tapping.’ This is a technique where thieves use portable NFC readers to skim card data or initiate small transactions from a distance. While modern security measures make direct theft difficult, the potential for unauthorized access to payment information or small fraudulent charges is real, especially in crowded public spaces.
5 Essential Protections Against Wallet Scammers
Fortunately, safeguarding your digital wallet is straightforward. Implementing these five strategies significantly reduces your risk:
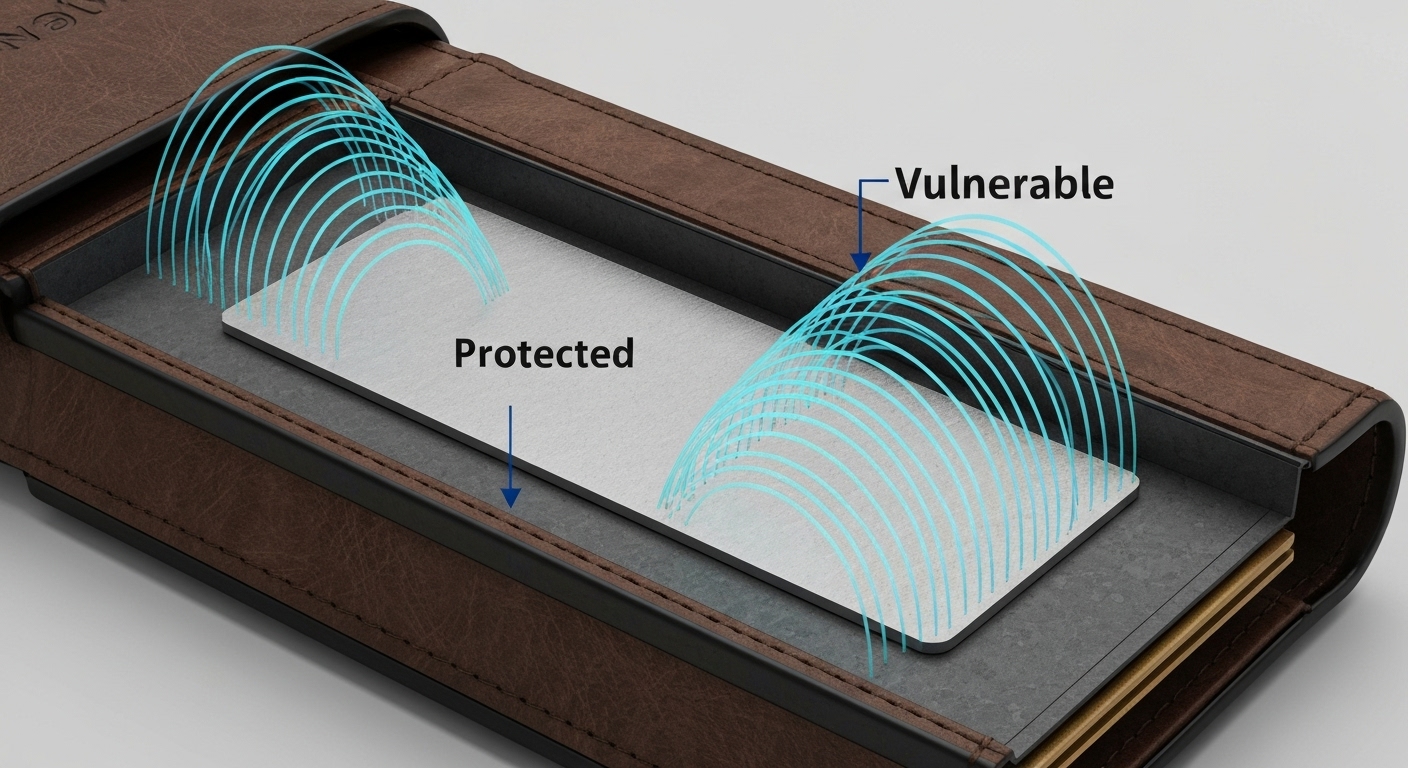
- Use an RFID-Blocking Wallet or Sleeve: The most direct defense is a physical barrier. Wallets and sleeves lined with RFID-blocking materials create a Faraday cage effect, preventing NFC signals from reaching your cards.
- Be Mindful of Crowded Areas: Thieves often operate in busy environments like public transport or concerts. Keep your wallet in a secure, less accessible pocket, or hold it closer to your body.
- Disable NFC When Not in Use (for Cards): Some contactless cards allow you to disable NFC functionality. While less common, check with your bank if this is an option for added security.
- Monitor Your Accounts Regularly: Set up transaction alerts with your bank or credit card provider. This allows for immediate notification of any suspicious activity, enabling quick action.
- Leverage Mobile Wallet Security Features: If you use Apple Pay, Google Pay, or Samsung Pay, take advantage of their built-in security. These platforms often use tokenization, meaning your actual card number isn’t stored on the device or transmitted during a transaction, adding a significant layer of protection.
Editor’s Take: The Evolving Arms Race
Contactless payment technology is a marvel of modern convenience, but it’s an ongoing arms race between innovation and exploitation. While banks and tech companies are constantly improving security protocols, the onus also falls on consumers to adopt basic protective habits. The ‘ghost tap’ threat, though perhaps overhyped by some, represents a tangible risk that demands proactive measures. Investing in a simple RFID-blocking wallet is a small price to pay for peace of mind in an increasingly connected world. We’ve seen similar security concerns emerge with the rise of smart home devices and IoT, highlighting a broader trend: as technology integrates deeper into our lives, so do the potential vulnerabilities.
This article was based on reporting from ZDNet. A huge shoutout to their team for the original coverage.